We often read, watch or hear about massive data breaches, where hackers have tunnelled through an organisation’s cyber defences and stolen sensitive personal information about millions of citizens and corporations.
In most cases, we become aware that an attack has occurred, but we rarely know what happens to the stolen data. Much of it is traded on the dark web to criminal syndicates, who use that information to target individuals for financial gain.
IFW Chairman Ken Gamble says major data breaches have exposed people all over the world to international cybercriminals.
“At IFW Global, we’ve acted rapidly in ransomware and business email compromise cases, tracing stolen funds to offshore accounts,” said Mr Gamble.
“In one case, we halted $1 million headed to Malaysia, freezing it through our foreign partnerships. While law enforcement might not pursue these funds, we do. We’re capable of stepping in and we can retrieve millions of dollars that might have been lost for ever.”
While law enforcement is bound by jurisdiction and politics, IFW Global can operate seamlessly across borders, even when governments won’t cooperate with one another. Our global network, free of political constraints, allows us to work directly with partners in any region, ensuring asset recovery and solutions even when official channels stall. In the private sector, our reach and speed are the difference between recovery and permanent loss.
IFW Global can:
- Investigate how stolen data is being used by criminal networks.
- Identify and attribute offenders involved in fraud and impersonation activity.
- Support victims and legal counsel in tracing funds and recovery efforts.
Find out more about IFW Global on our YouTube channel
Eye on Optus
Between October 2019 and September 2022, one of Australia’s largest telecommunications companies, Optus, failed to implement adequate cybersecurity measures, ultimately compromising the personal data of approximately 9.5 million Australians
On 8 August 2025, in submissions to the Federal Court, the Australian Information Commissioner (OAIC), the company did not take reasonable steps to protect customer information, raising serious concerns about corporate accountability in the digital age.
Despite being a high‑profile organisation and an obvious target for cybercriminals, Optus did not sufficiently address the risks associated with storing vast amounts of sensitive data. This oversight proved costly.
In September 2022, a cyberattack exposed highly sensitive customer information, including names, dates of birth, phone numbers, email addresses and, in some cases, passport numbers, driver’s licence details, Medicare numbers, and birth certificate data. The scale and sensitivity of the breach made it one of the most significant data leaks in Australian history.
Let’s pause on Optus for a moment and look at the broader picture.
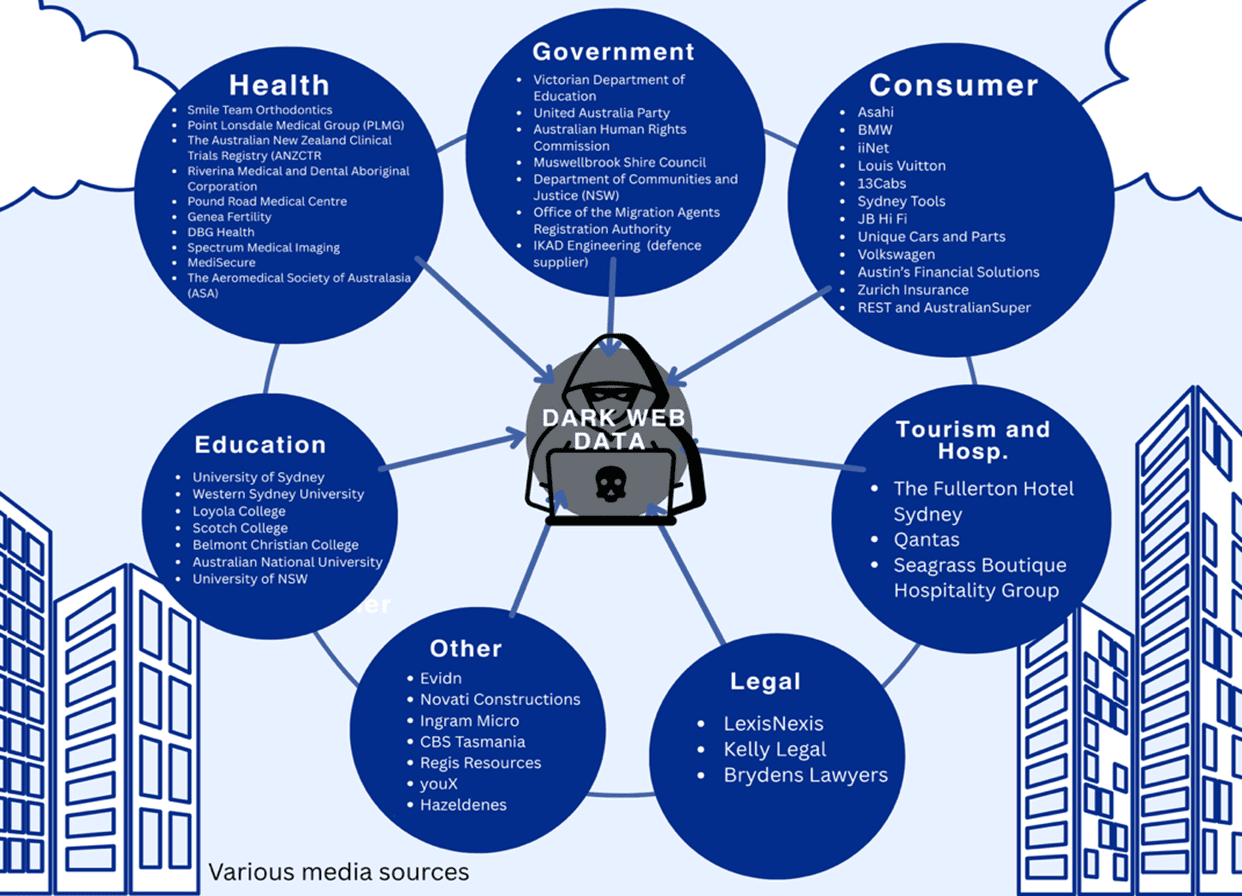
Who’s been hit in Australia?
As best we could, IFW Global compiled a list of the most recent Australia-based orgnasiations that have been exposed by data breaches. It makes for confronting reading.
The list includes companies and corporations from all sectors of society, where highly sensitive information was obtained by criminals syphoned to the dark web for criminal enterprises to feast on.
From the beginning of 2025 until mid-March 2026, we counted nearly 100 companies that have made headlines over data breaches. These are just media reported breaches.
The names on the list range from nationally recognised organisations to local enterprises, but the common theme is clear: we are all exposed.
“What makes modern scams so effective is that they don’t feel random. When a criminal already knows your name, email, or recent activity, the approach feels legitimate,” IFW’s Global Director of Investigations Allan Watson said.
“Organisations need to understand that once data is compromised, control is lost — and the consequences can surface months or even years later.
“Now AI is allowing criminal to not only churn through the data at a faster pace for faster results for them, but it’s allowing them to become more creative on how they use that data to trick their targets.”
Huge failures at Optus
Investigations into the breach revealed that Optus had failed not only in securing this information but also in recognising and preparing for the likelihood of such an attack. They failed to address how much of a risk they were being a high profiled victim themselves.
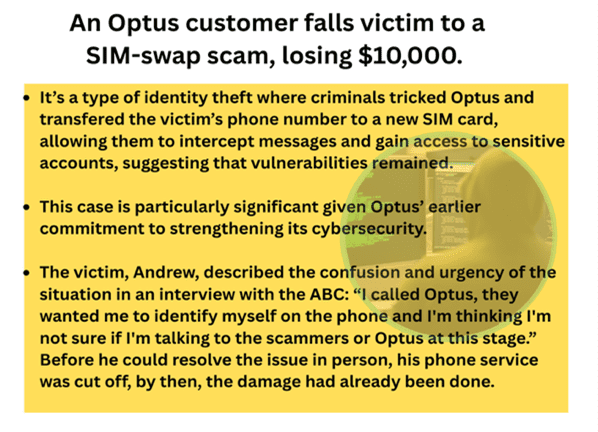
While Optus initially described the breach as “sophisticated,” findings from the Australian Communications and Media Authority (ACMA) suggested otherwise. The attack reportedly required minimal technical expertise and was carried out through basic trial-and-error methods, further highlighting the preventable nature of the incident.